POSITION SECURITY AND RISK MANAGEMENT IN A STRATEGIC BUSINESS CONTEXT
Establish a cybersecurity framework to build a strong foundation for your overall security posture
Security & risk management for an evolving threat landscape
Aspire aligns security strategy, risk management and compliance with your business objectives.
In today’s digital world, securing the data, applications, and infrastructure that organizations rely upon for business is more critical than ever. IT leaders must assure effective security and risk management practices are in place to meet compliance requirements and support the organization’s strategic initiatives. Recent surveys place the average cost of a data breach at $3.86 million, making the stakes high. The challenge is threats are constantly evolving and can surface from anywhere inside or outside the company. Compounding the problem, many organizations lack the in-house security expertise to implement a successful information security strategy and don’t know how to get started.

By putting security and risk management in a strategic business context, Aspire empowers IT and business leaders to manage the constant security evolution with a straightforward, repeatable process. Aspire security consultants start with a cybersecurity framework to help establish a strong foundation for an effective security program. From there our practitioners provide consulting and assessment services, customized based on your maturity, following a proven repeatable process.
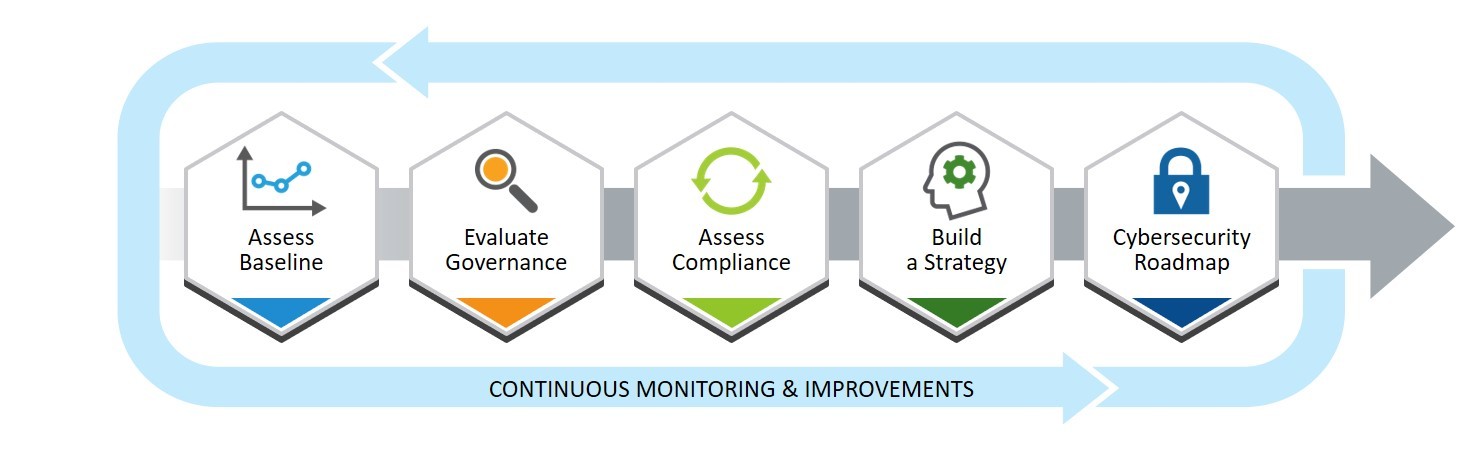
This approach helps IT and business leaders take a more holistic view of security technologies and processes – ensuring appropriate and effective safeguards are in place for even the most complex enterprise. The output is a security roadmap providing a strategic plan to close gaps and identify the resources, processes, and solutions needed to meet compliance mandates and improve the overall security posture.
Aspire Security and Risk Management services are available in flexible options:
Virtual CISO
A flexible, customizable annual service delivering deep, executive-level security and risk management guidance to shape, define and lead the organization’s overall Security Program.
Security Consulting and Assessment services
Efficient and cost-effective tactical engagements to identify gaps and issues, measure risk, and recommend corrective actions. These services include:
- Cybersecurity Framework
- Governance
- Compliance Readiness
- Policy Creation
- Risk Management
- Executive Communications
- Penetration Testing
- Vulnerability Assessments
- Web Application Assessments
- Wireless Security Assessments
- Security Configuration Review
Let us help you get started today.
Press Release
 Aspire Technology Partners Achieves Recognition in CRN 2022 MSP 500 Security 100 List for Seventh Consecutive Year
Aspire Technology Partners Achieves Recognition in CRN 2022 MSP 500 Security 100 List for Seventh Consecutive Year
Aspire Technology Partners has been named to the CRN 2022 Managed Service Provider (MSP) 500 list in the Security 100[...]

